OS Design and Implementation: (Week 4) - Trap
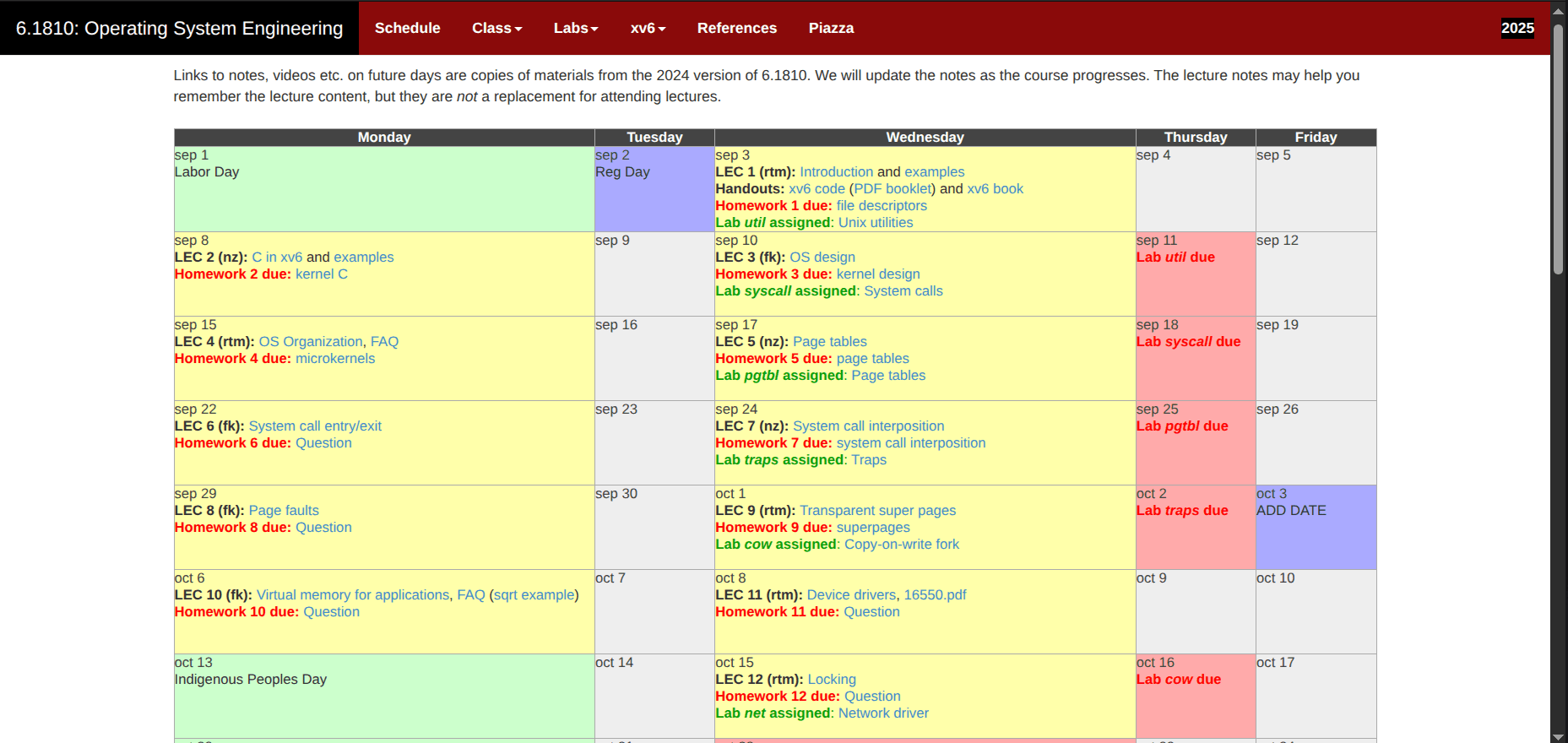
MIT 6.1810 Fall2025 Course - Week 4: Trap
Software Developer | Love Low Level Eng. | Python, Javascript, C, Linux I'm learning backend development and system programming.
Lecture
xv6 Book; Chapter 4 - Traps and system calls: https://pdos.csail.mit.edu/6.1810/2025/xv6/book-riscv-rev5.pdf
The lecture in the 4th week was about Traps.
A trap is an event that causes the CPU to switch from its current task to specific code in the kernel space to handle the event. There are three types of traps:
syscall: user space code asking the kernel (through the ecall instruction) to perform an action
interrupt: when a device requests attention, like an I/O operation with a disk
exception: when something goes wrong in either the kernel or user space.
Anyway, there are common operations that need to be done when a trap occurs:
Save the current state of the CPU and what's being executed (registers, memory, etc.)
The CPU enters supervisor mode.
The kernel performs appropriate checks (permissions, security, etc.)
Jump to the kernel code (handler) that will handle the trap.
Restore the saved state.
Resume the execution of the running code.
Saying it like this makes it sound easy, but it's more complicated. For example, in the case of Xv6, process state saving is written directly in RISC-V assembly language, and there can be more layers between when the trap occurs and when the process execution resumes.
In the case of a syscall, here is a path in the code:

Where trampoline is a memory space within the process address space, mapped directly to the same memory space inside the kernel address space, containing the code to enter and exit the kernel.
You can find more details in the book: https://pdos.csail.mit.edu/6.1810/2025/xv6/book-riscv-rev5.pdf
There was a lot of RISC-V assembly code to read at this point 😭
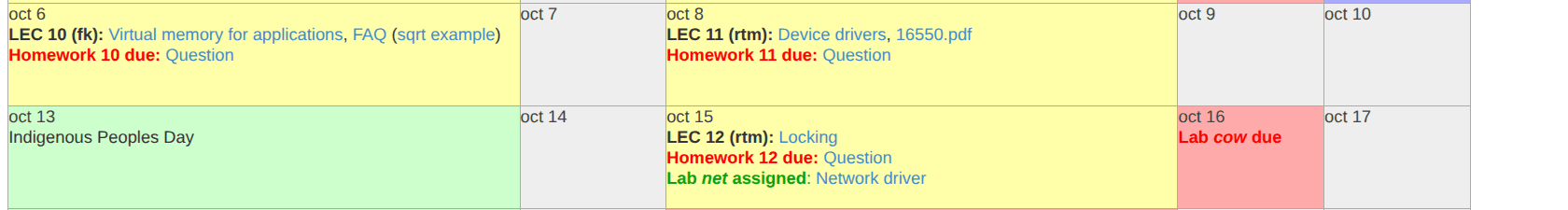
Labs
There are two labs to complete - https://pdos.csail.mit.edu/6.1810/2025/labs/traps.html:
Backtrace: A backtrace, also known as StackTrace, reconstructs the call history by going through a chain of stack frames. Each frame stores a return address and a pointer to the caller's frame. By starting with the frame pointer (s0) and following these links upward, you can identify and print the return address for every function in the current execution path.
Alarm: You will implement a feature in xv6 that periodically interrupts a process after a set amount of CPU time, serving as a basic foundation for user-level interrupt and fault handlers. Your solution is complete once it successfully passes the
alarmtestandusertests -qverification suites.
Unlike in week 3, I completed these two labs this time. A big thank you to https://github.com/Miigon for having solutions for some labs of this course, but for the 2020 version "https://github.com/Miigon/my-xv6-labs-2020." It really helped me after spending about 2 weeks working on these labs. My challenge was reading the lectures, the book, and trying to understand the code and explanations on my own, so it wasn't always easy. Having a repository to check when I'm stuck or facing difficulties is really helpful.
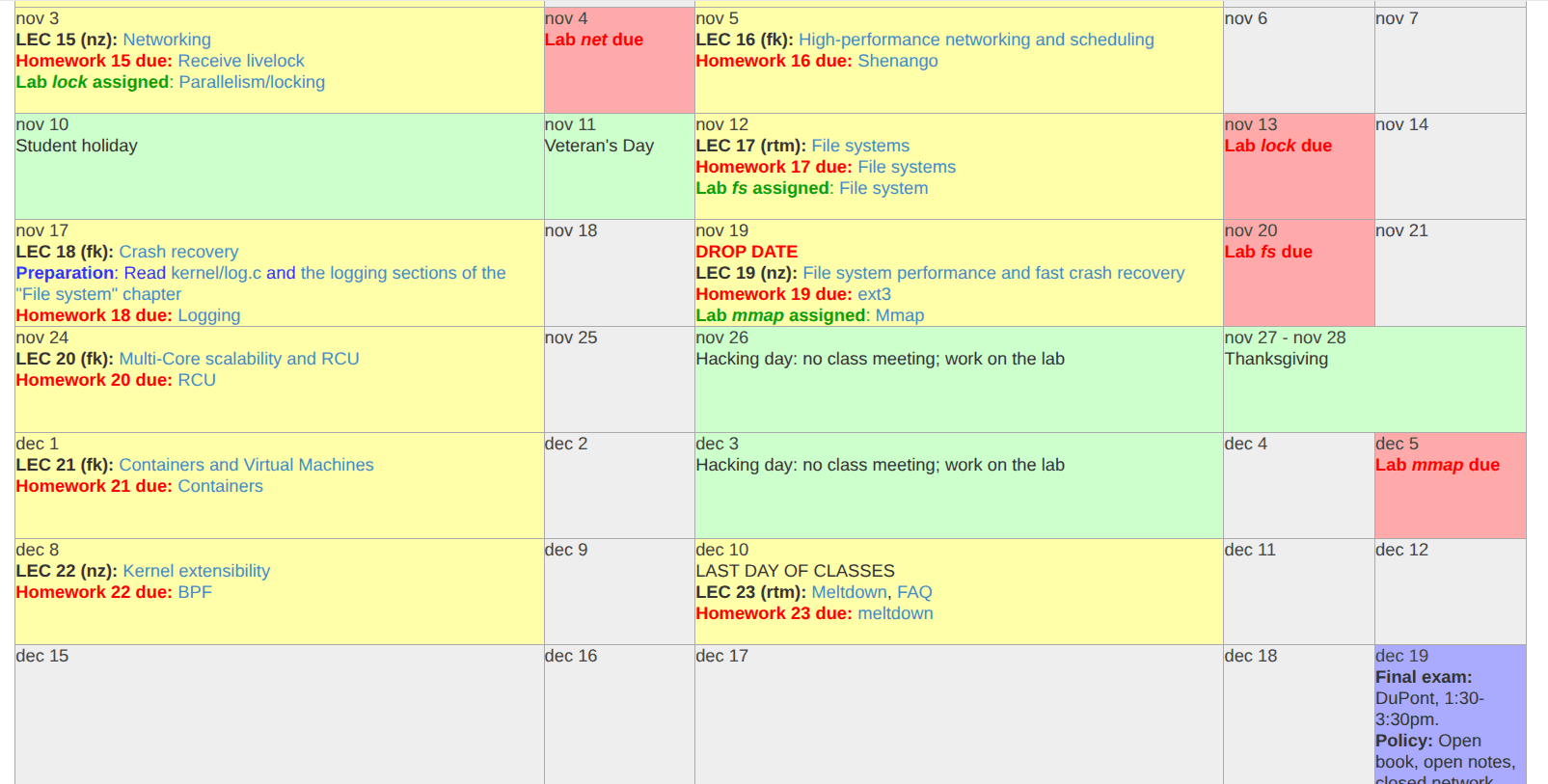
Next week
Next week is about Page faults.
By the way, here's my GitHub repo for the lab course: https://github.com/TawalMc/MIT-6.1810Fall2025-xv6