OS Design and Implementation: (Week 2) - Syscall
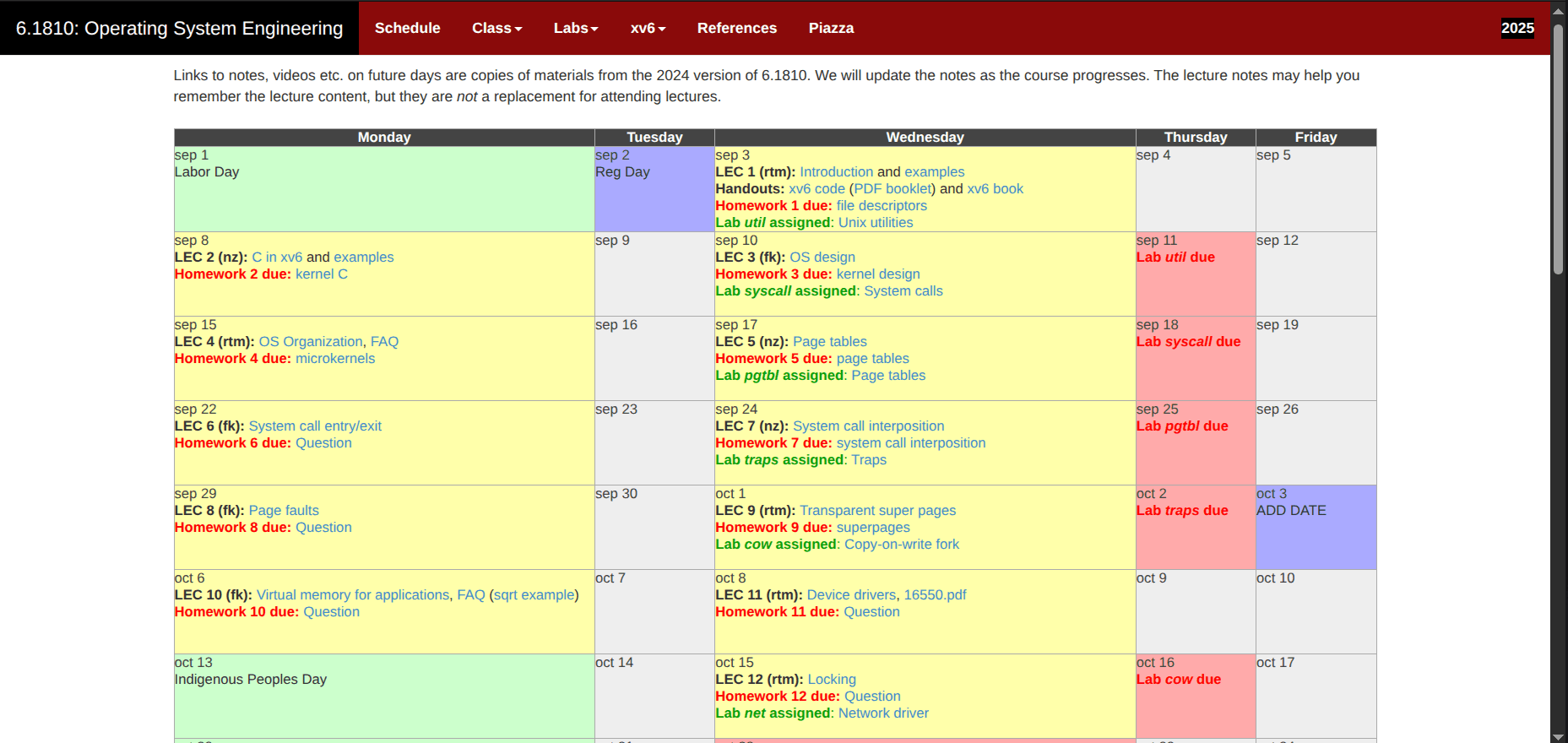
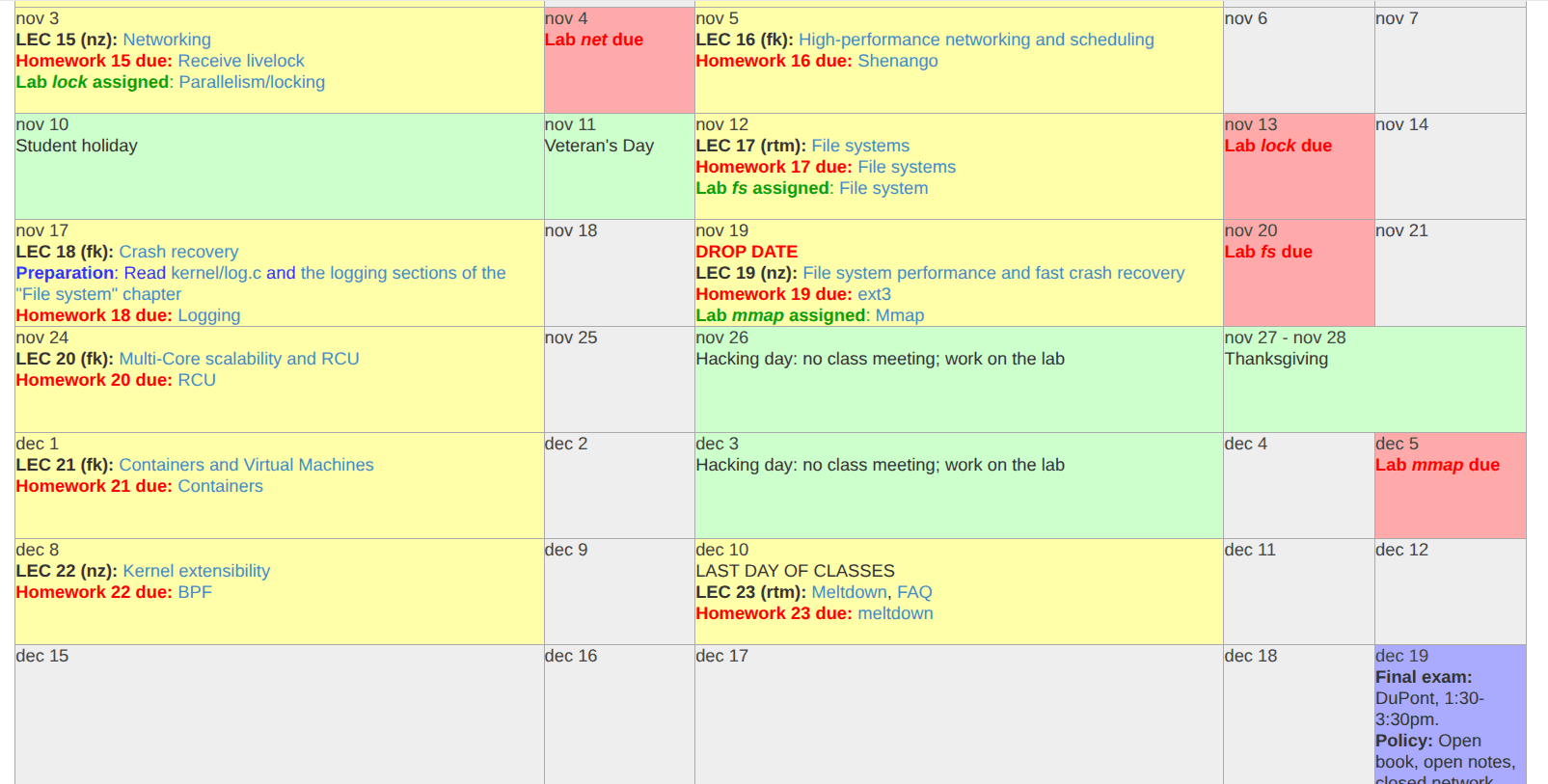
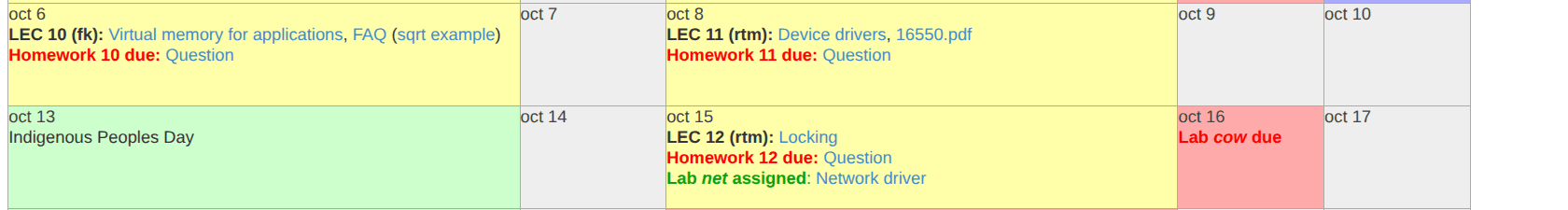
MIT 6.1810 Fall2025 Course - Week 2: system calls
Software Developer | Love Low Level Eng. | Python, Javascript, C, Linux I'm learning backend development and system programming.
It took me almost three weeks (nights and week-end) to read Chapter 2 of the xv6 book: Operating System Organization, study the xv6 code (process and system calls), and finish the assignments on system calls.
This chapter covers the organization of the operating system:
There is a separation between the kernel and user space: user space code does not directly call kernel space code.
Processes are isolated, with each process running as if it has its own dedicated CPU and virtual memory, which is its own memory space (it cannot access memory outside this space without requesting more).
The underlying architecture (CPU) provides a system call mechanism (RISC-V uses the ecall instruction) to switch from user code to kernel code.
The kernel performs checks when a system call is triggered to ensure the operation is allowed and the correct arguments are passed.
Every system call, like read for example, is assigned a number (the read system call number in xv6 is 5) that the kernel uses to identify which system call the user code triggered.
And more... I'll explain "System Call" in more detail in my next blog post.
And the labs? I spent most of my time trying to understand the assignments and figuring out where to start. Here are the labs:
Implement a system call called “interpose” that limits the use of system calls based on a bitmask passed as an argument to interpose.
Exploit a vulnerability in xv6 that lets a process read data from another process's virtual memory. This lab helps illustrate why kernel code must be well-written.
Currently, I'm getting hands-on experience with GDB for more effective debugging of the C and kernel code.
Next week, I'll start Week 3: Page Tables.